S3 Access Points
code for article pfeilbr/s3-access-points-playground
learn S3 Access Points
Be sure to review Access points restrictions and limitations before considering for a use case.
Feature Overview
- Access points are unique hostnames
- enforce distinct permissions and network controls for any request made through the access point.
- Customers with shared data sets scale access for hundreds of applications by creating individualized access points with names and permissions customized for each application.
- access point can be restricted to a VPC to firewall S3 data access within customers’ private networks
- AWS Service Control Policies can be used to ensure all access points are VPC restricted.
- no longer have to manage a single, complex bucket policy with hundreds of different permission rules that need to be written, read, tracked, and audited. With S3 Access Points, you can now create application-specific access points permitting access to shared data sets with policies tailored to the specific application.
Example
Policy
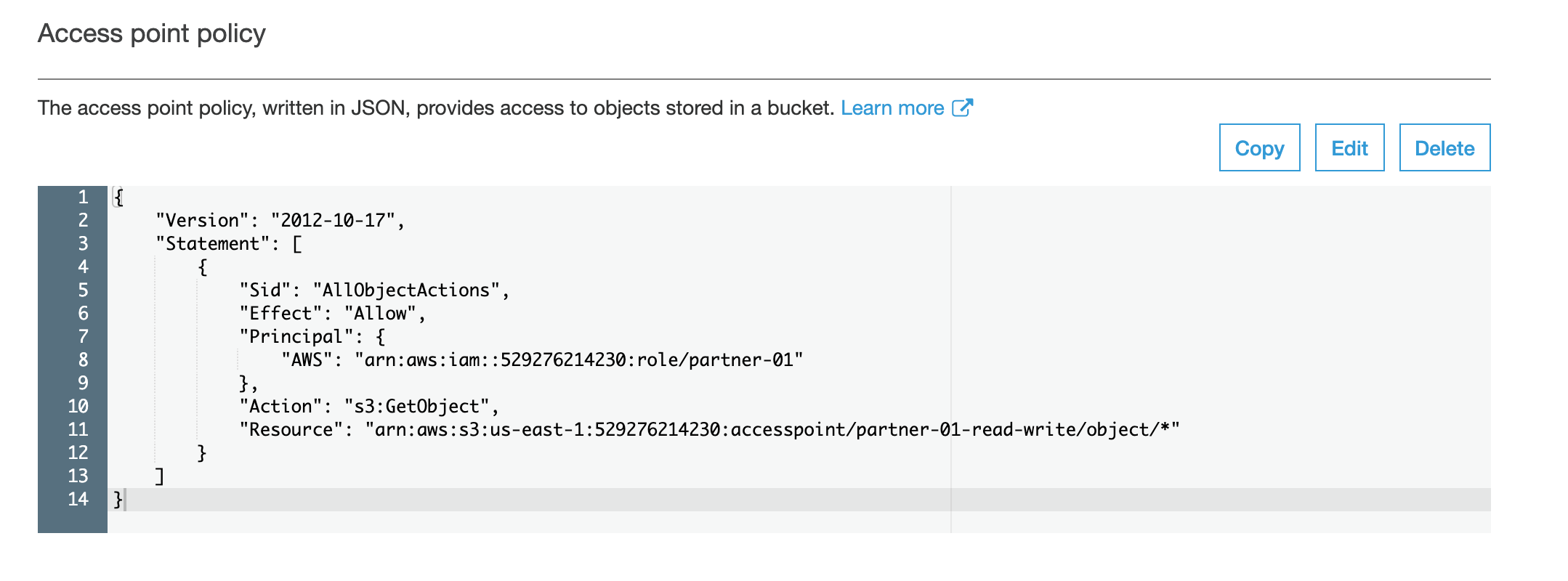
limit access to partner-01 role
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "AllObjectActions",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::529276214230:role/partner-01"
},
"Action": "s3:*Object",
"Resource": ["arn:aws:s3:us-east-1:529276214230:accesspoint/partner-01-read-write/object/*"]
}
]
}
Access Point Hostname
https://partner-01-read-write-529276214230.s3-accesspoint.us-east-1.amazonaws.com
Example Usage
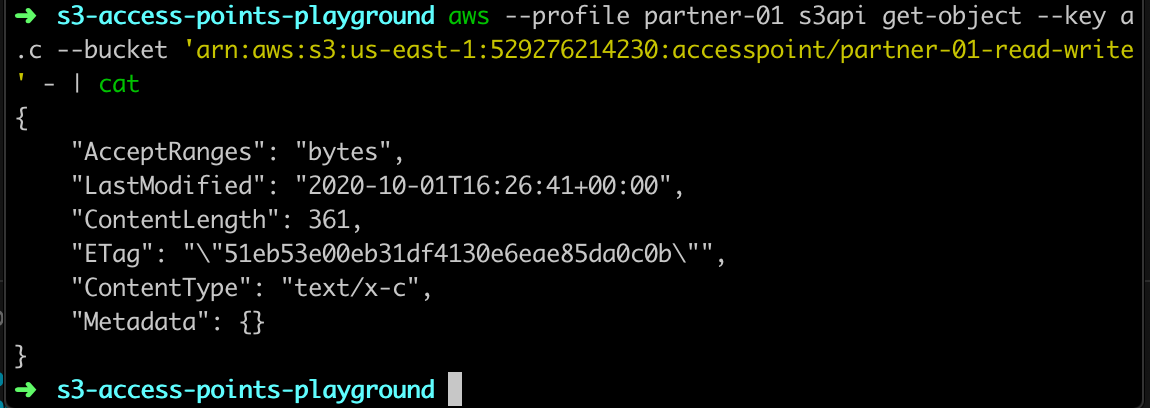
# get `a.c` using `partner-01` role
aws --profile partner-01 s3api get-object --key a.c --bucket 'arn:aws:s3:us-east-1:529276214230:accesspoint/partner-01-read-write' -
Resources
- S3 | Access Points
- Easily Manage Shared Data Sets with Amazon S3 Access Points
- Access points restrictions and limitations
- Amazon S3 Access Points - Tutorials Dojo
Screenshots
get via access point example
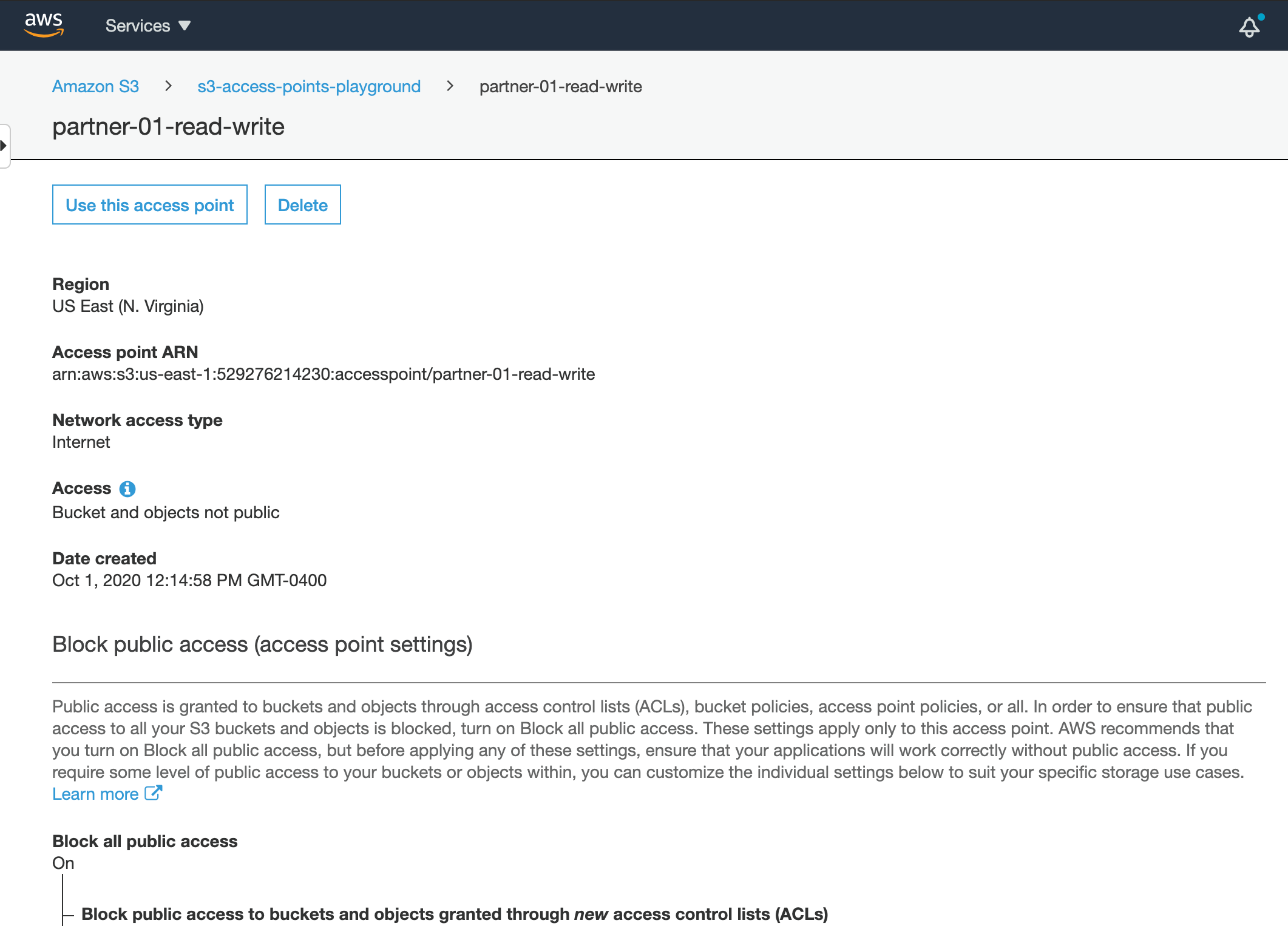
access point details
access point policy
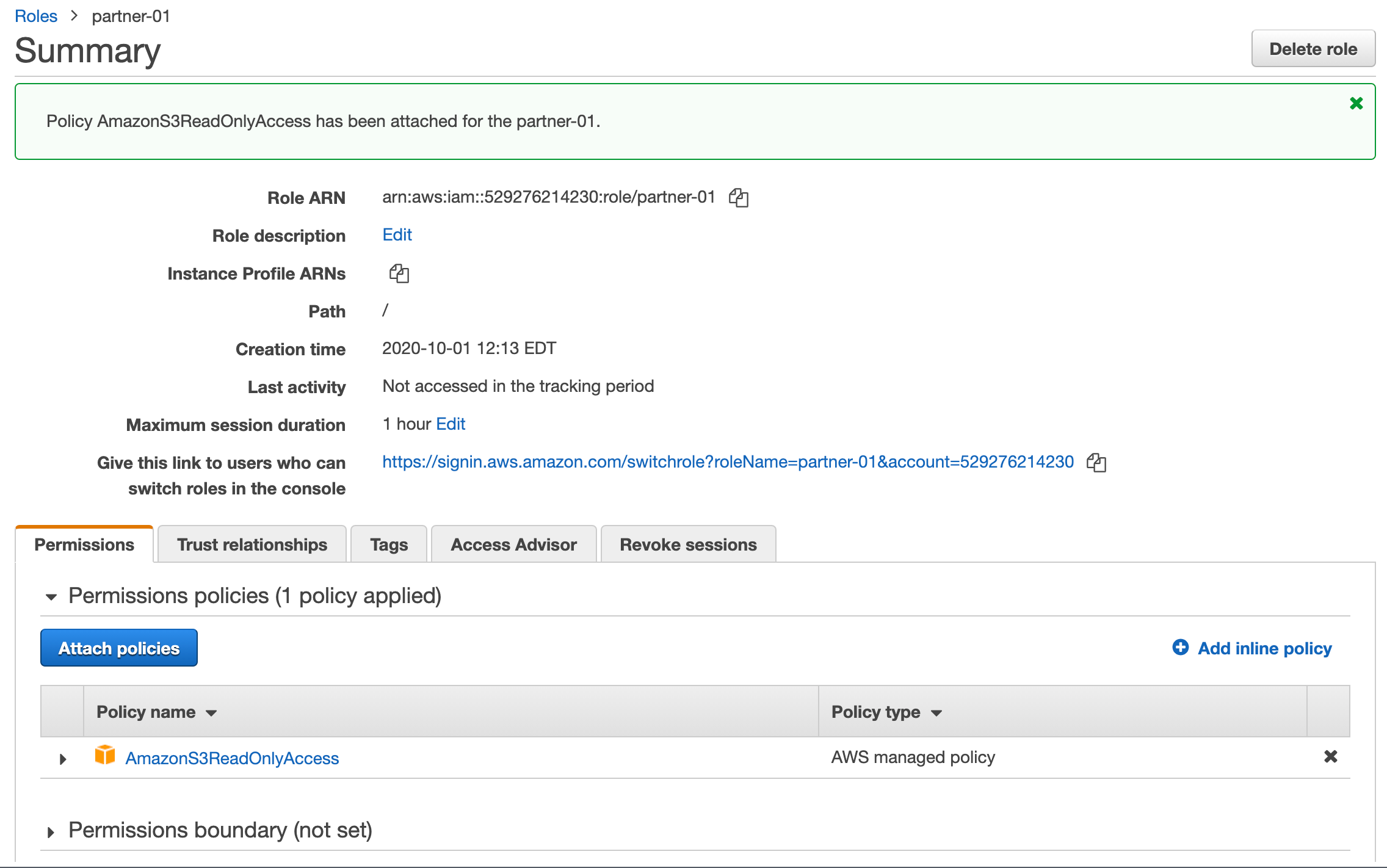
partner-01 role (requires S3 read permissions)
Scratch
cd ~/tmp
aws s3 cp a.c s3://s3-access-points-playground/
# verify assume role works
aws --profile partner-01 sts get-caller-identity
aws --profile partner-01 s3api get-object --key a.c --bucket 'arn:aws:s3:us-east-1:529276214230:accesspoint/partner-01-read-write' -
aws --profile partner-01 sts get-caller-identity